JeremyNzl:No ads on youtube or tvnz, haven't tried FB yet.
<The parallel upstread dns looks good also.
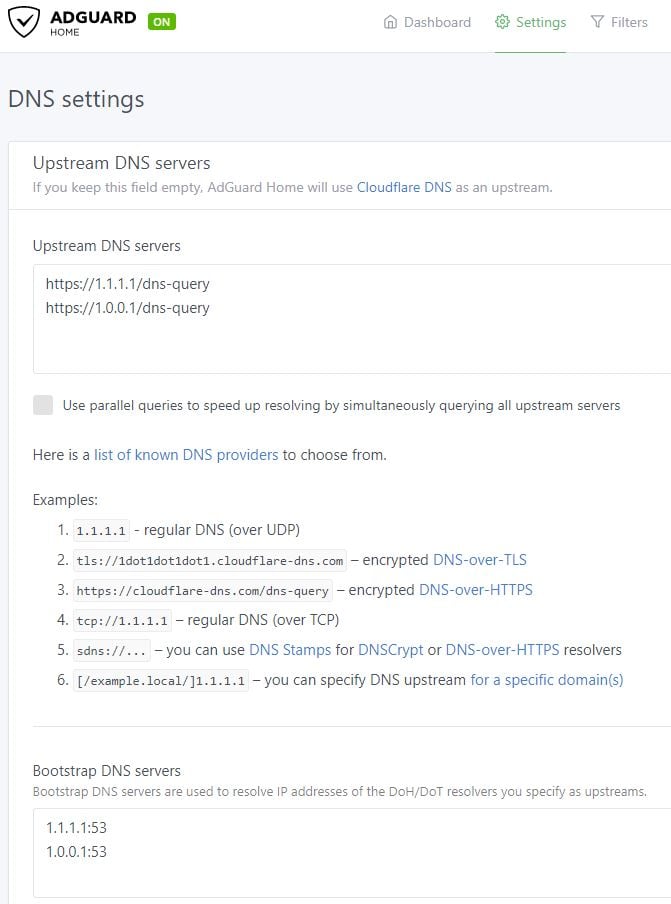
Do you know if it blocks ads on YouTube for android tv? Can you configure your own dis forwarder? I chain mine off getflix so I get ad blocking and BBC iPlayer on my Nvidia Shield.