|
|
|
timmmay:
RFC9375 says to use home.arpa. I switched to that when I moved pihole to docker.
This would then be the safest method for small business and home networks that are not being expanded.
reven:
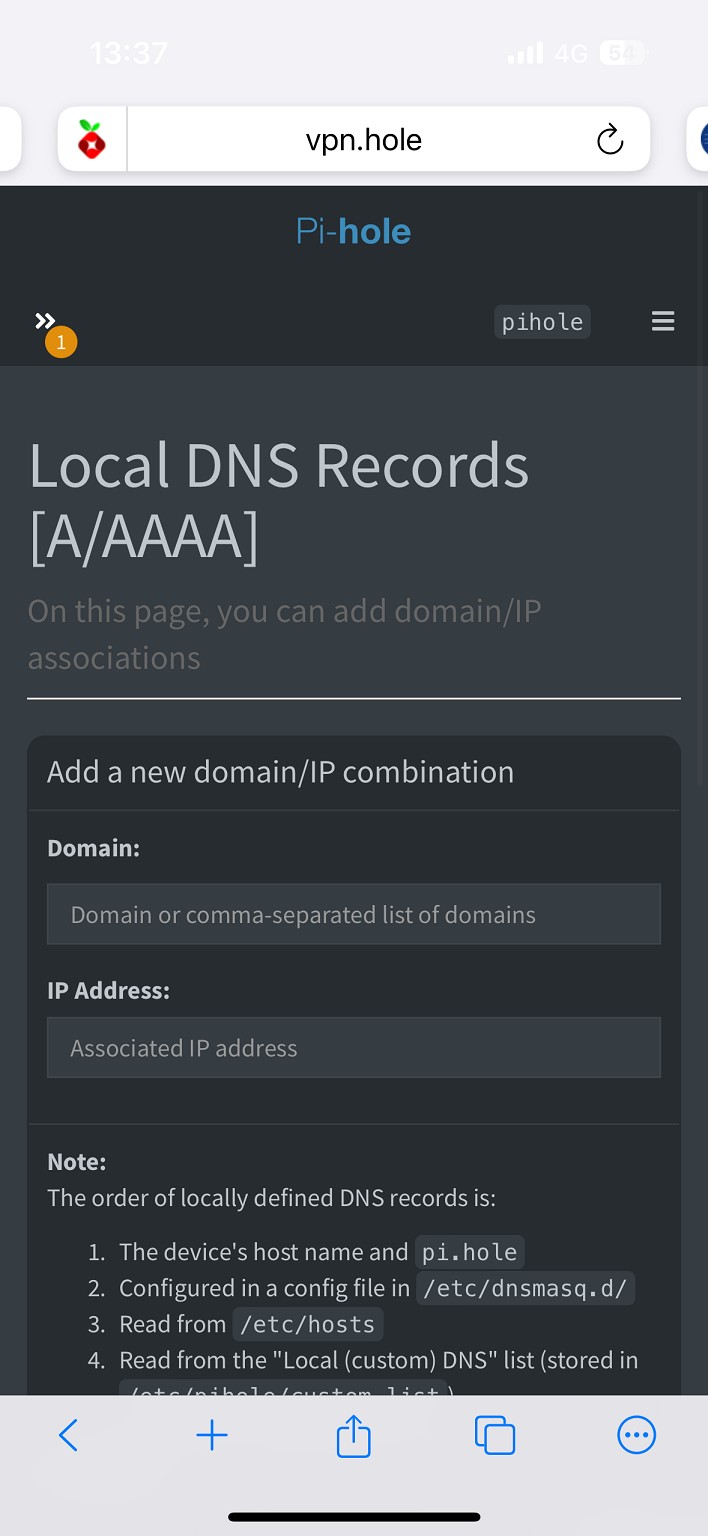
I believe this fixes it if using pihole, under "Domains" adding a regex blacklist.
nslookup returns 0.0.0.0 now for me, vs before it would return the "2001:19f0:6c00:1b0e:5400:4ff:fecd:7828 / 45.76.93.104".
looks like action has been taken
Any views expressed on these forums are my own and don't necessarily reflect those of my employer.
nztim:
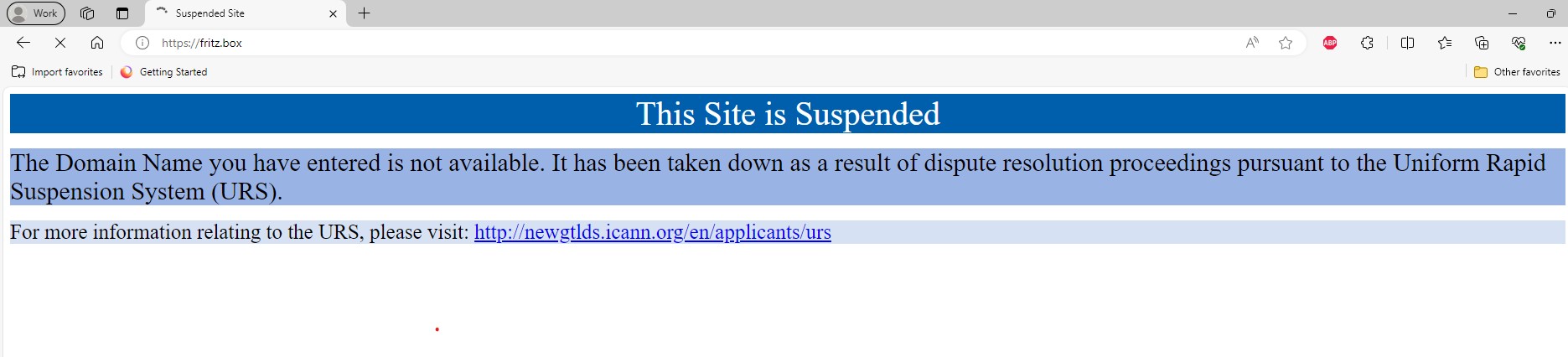
looks like action has been taken
This is temporary. AVM has had the domain name blocked and still has to go through ICANN's URS process.
I've noticed my Synology NAS was still trying to reach multiple domains with the fritz.box domain attached. These lookups were all blocked with Cloudflare Zero Trust Gateway but... Because these lookups were returning NXDOMAIN (0.0.0.0) the NAS was getting errors when checking for updates or trying to backup the configuration.
This was a serious risk, as anyone controlling any of these fritz.box subdomains could easily setup a honeypot for Synology NAS users:

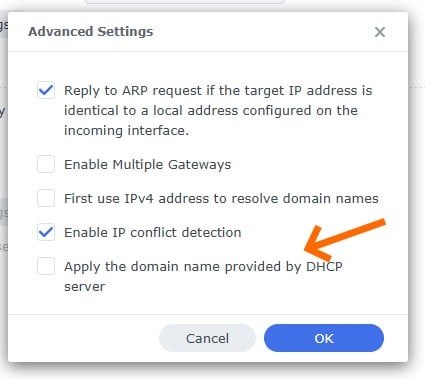
In the end I figured that a DNS option have to be changed to stop these. In the network tab of the NAS configuration there's an Advanced DNS option and this needs to be unchecked:
Referral links: Quic Broadband (free setup code: R587125ERQ6VE) | Samsung | AliExpress | Wise | Sharesies
Support Geekzone by subscribing (browse ads-free), or making a one-off or recurring donation through PressPatron.
|
|
|
