|
|
|
No accountability for him. You get yourself cancelled if you are almost anyone else saying that absolute tripe.
He digsusts me.
SirHumphreyAppleby:
clinty: Crowd strike have blogged the technical details of what happened
A bit light on detail there. The crash resulted from an access violation, dereferencing an incorrectly initialised pointer (not a NULL pointer as some reports indicate).
The code which caused the crash may well have been years old and only triggered by the new configuration.
Well that would be splitting hairs.
An uninitialized pointer is a pointer that has been declared but not assigned a valid memory address.
Is more or less the same as...
A null pointer is a pointer that is explicitly assigned the value of NULL to indicate that it intentionally points to no valid memory location.
How do you know it was an Access Violation?
K8Toledo: Well that would be splitting hairs.
An uninitialized pointer is a pointer that has been declared but not assigned a valid memory address.
Is more or less the same as...
A null pointer is a pointer that is explicitly assigned the value of NULL to indicate that it intentionally points to no valid memory location.
Not necessarily. Some systems map the zero page to valid memory so NULL pointer derefs can be managed in a way other than producing a segfault.
Also, if you're going to get pedantic, NULL pointers have special semantics in C/C++.
K8Toledo: Well that would be splitting hairs.
An uninitialized pointer is a pointer that has been declared but not assigned a valid memory address.
Is more or less the same as...
A null pointer is a pointer that is explicitly assigned the value of NULL to indicate that it intentionally points to no valid memory location.
neb:
Not necessarily. Some systems map the zero page to valid memory so NULL pointer derefs can be managed in a way other than producing a segfault.
Well I would hope all systems map the zero page to valid memory, because if not - something is very, very wrong. :)
I think you may be confusing "null" pointers with the zero page or zeroed (free) memory? If not you'll need to expand on your comments above because I don't know what you mean.
Pointers are translated to real memory addresses by the CPU. But a NULL pointer is a pointer that doesn't point to any memory location at all.
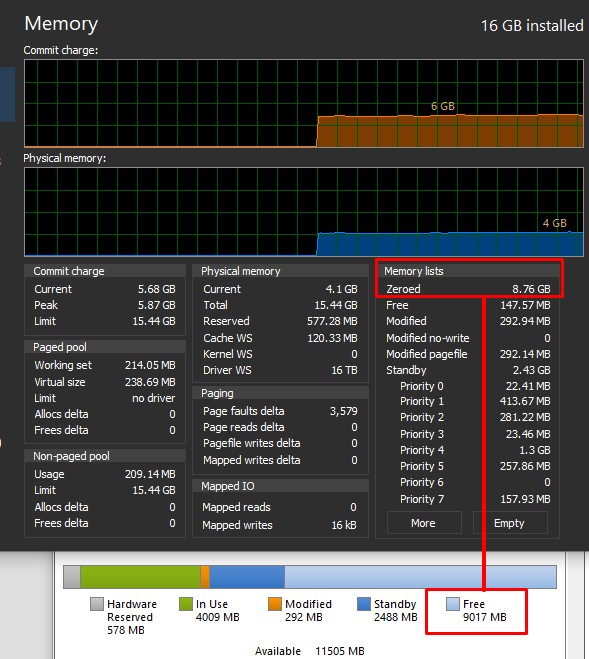
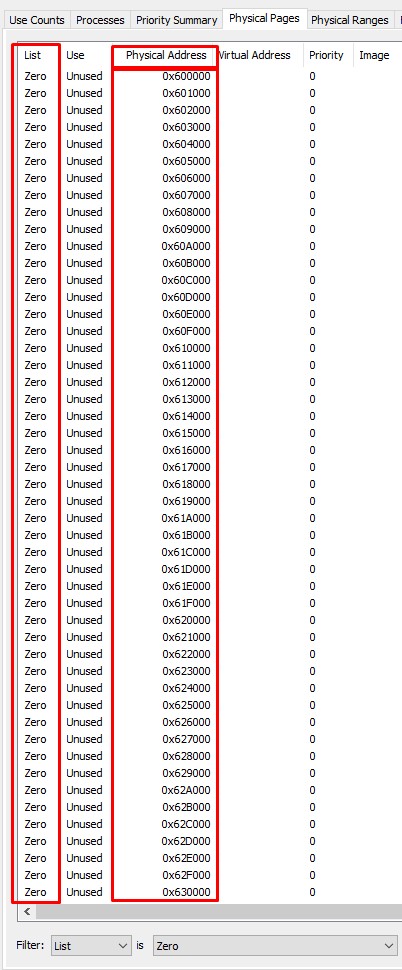
Zeroed pages are memory addresses emptied of previously stored data and filled with zeros, available for immediate use. Zeroing prevents processes seeing data stored by earlier processes that used that memory address.
The zero page is just the first address in RAM, as mapped by the CPU during the boot process. Both zeroed pages and zero page should map to valid memory addresses in RAM (or page file if a PF exists).
It never ceases to amaze me the number of developers and coders, particularly those schooled by Microsoft that don't understand CPU Address Translation and assume that all pointers are valid addresses in RAM.
And how am I being pedantic.....?
The desktop is 4670K with 578Mb reserved for the onboard GPU. No pagefile.
On the right you can see the zeroed "pages" are real addresses in RAM
K8Toledo:
How do you know it was an Access Violation?
Someone posted a crash dump. The crash occurred dereferencing a non-NULL pointer to invalid memory, resulting in error code 0xc0000005 (Access Violation).
The memory address was quite low, suggesting an offset added to a NULL pointer. C/C++ programmers often checks for NULL input, but if you have an error resulting in a NULL pointer, fail to check for it and immediately add an offset (e.g. fixed header size), later code is unlikely to pick it up.
johno1234:Wheelbarrow01:
Overall I’m really pleased with how my first day working at Crowdstrike went yesterday.
A couple of minor mistakes, no biggie…
😂🤣😂
It's the best job I've had since that one where I did maintenance work on Northland power transmission towers!
you really like end of the week tasks….was that job before the one you had at foodstuffs when there was a dodgy software update rolled out on a Friday afternoon which crippled each and every new world and pak n save…
Well, I didn't even know we used this thing at work, but everything's down and evidently IT must have been accosted on the way into the building because they ain't here yet...
Correction: It seems to be affecting maybe 10% of computers here.
CrowdStrike IT Outage Explained by a Windows Developer
Behodar:
Well, I didn't even know we used this thing at work, but everything's down and evidently IT must have been accosted on the way into the building because they ain't here yet...
I think they've been there already and decided to do a runner.
Referral links: Quic Broadband (free setup code: R587125ERQ6VE) | Samsung | AliExpress | Wise | Sharesies
Support Geekzone by subscribing (browse ads-free), or making a one-off or recurring donation through PressPatron.
One of the guys turned up a few minutes ago, someone's laptop in hand. I think it's going to be a busy day for him!
BarTender: I do firmly blame much of the situation on Microsoft being unable to supply an OS with sufficient hardening steps that a separate vendor is required for EDR rather than the OS being sufficient.
I also blame IT Security management requirements in some industries such as Telco, Fintech, Medical and Aviation that rightfully have vulnerability policies that if a zero day drops it needs to be patched immediately before you get pwned and having mitigation tools to reduce your risk surface on the unknown unknowns. All I need to say is “log4j, OpenSSL shell shock and xz” where similar issues that impact Linux hosts.
The main difference is where complexity and the environment grows and managers don’t want to pay staff to be available 24/7 for remediation that tools will come in place to replace humans with automation… and when those tools are deployed at scale this could very easily have happened on any platform.
Until there is a point where human intervention is considered an asset not a liability in critical technical infrastructure services I can see this happening again. Perhaps not on this scale… but I can see how it could easily happen again even without the possibility of a supply chain attack.
As you state, the foundational cause is the architectural decisions made by Microsoft around the kernel and how applications interact/control plain allowing an application to brick and O/S vs. terminate/disallow. Dont be fooled into believing this is only a MS risk/issue..... Architecture always is a trade off of many things.
There's multiple lessons here for all, from Vendors, customers, MSPs etc. - As always Security is about defense in depth, layers, acceptable risk, $$, culture, diversity of AV products etc.
Nick
https://nick.mackechnie.co.nz | NZ ISP latency monitoring - https://smokeping.thenet.gen.nz
Apparently it's not the first time that Crowdstrike has pushed out updates without testing them. Apparently they learned nothing last time!
Behodar:
Apparently it's not the first time that Crowdstrike has pushed out updates without testing them. Apparently they learned nothing last time!
As with all things, when the consequences outweigh the benefits, then action and change occurs. Until then, BAU.
If they get sued, and they lose, and claim on their insurance, they will either be uninsurable or insured on a much more restrictive set of policies which ensure change management is done differently.
There was language in a customers recent insurance renewal, which covered off change management and was at least 6 questions. It even covered third party IT changes!
Well Southwest Airlines dodged a bullet
They must be happy :-)
|
|
|
