Perhaps another daft noob question .... so forgive me, but here goes...
Background:
- I've configured an ER-X with VLANs on switch0 as VLAN 1 and for IoT devices as VLANs 3, 4 & 7, eg Chromecast, Apple TV, Ezviz cams, with PVIDs and VIDs set per eth interface
- The IoT devices are Cat 6 wired via USW Flex Minis with ports profiled for the respective VLANs.
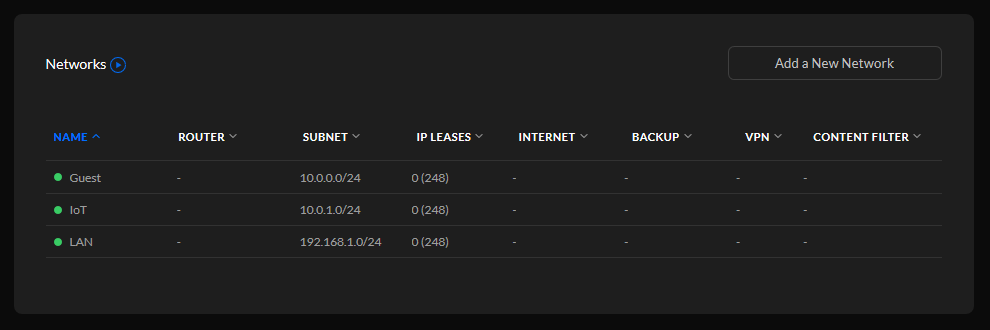
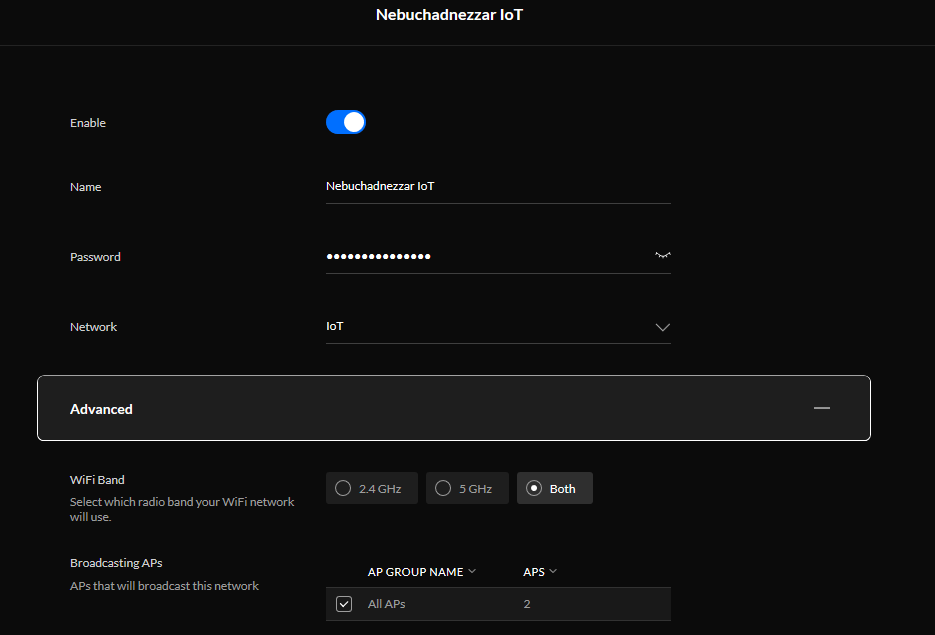
- I've then created "VLAN Only" networks in Unifi Controller for each VLAN, with firewall rules configured to prevent the IoT devices "leaking"
- The ER-X has its stock WAN firewall rules created by the WAN+2LAN2 Wizard
Issue:
- Everything appears to work fine, but when I audit the firewalls by giving my iMac a static IPA on any of the VLAN subnets, I can still ping the main LAN - which shouldn't happen if the firewalls were properly doing their thing per what I thought was a correct configuration.
Question:
- Per the headed subject matter, is it OK to mix system management like this with the ER-X essentials configured on EdgeMax OS (ver 2.0.9), and the VLAN ports and associated firewalls configured on Unifi Controller (ver 6.0.43)? I've assumed it is OK as this is exactly what I do on other systems in other circumstances with ER-x's and UAPs. If it is OK I'll have to dive deeper into the firewall on the Controller and get it properly sorted in this case; if not, I'll scrap the Controller VLAN configuration of firewalls and reconfigure the VLAN firewalls in EdgeMax OS.
Thanks in anticipation.