via Ars Technica
Hardware manufacturer Asus has released updates patching multiple critical vulnerabilities that allow hackers to remotely take control of a range of router models with no authentication or interaction required of end users.
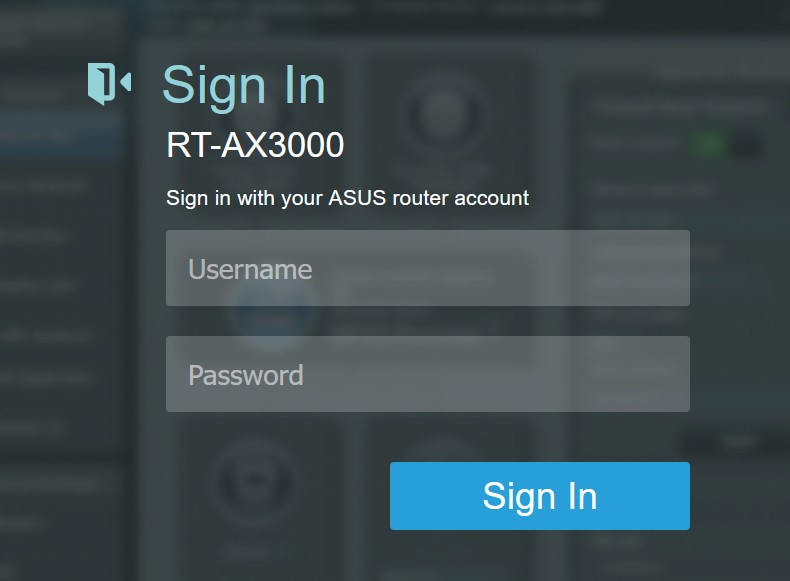
The most critical vulnerability, tracked as CVE-2024-3080 is an authentication bypass flaw that can allow remote attackers to log into a device without authentication. The vulnerability, according to the Taiwan Computer Emergency Response Team / Coordination Center (TWCERT/CC), carries a severity rating of 9.8 out of 10. Asus said the vulnerability affects the following routers:
Model name Support Site link
XT8 and XT8_V2 https://www.asus.com/uk/supportonly/asus%20zenwifi%20ax%20(xt8)/helpdesk_bios/
RT-AX88U https://www.asus.com/supportonly/RT-AX88U/helpdesk_bios/
RT-AX58U https://www.asus.com/supportonly/RT-AX58U/helpdesk_bios/
RT-AX57 https://www.asus.com/networking-iot-servers/wifi-routers/asus-wifi-routers/rt-ax57/helpdesk_bios
RT-AC86U https://www.asus.com/supportonly/RT-AC86U/helpdesk_bios/
RT-AC68U https://www.asus.com/supportonly/RT-AC68U/helpdesk_bios/
The Ars link also has details on some other vulnerabilities in other older routers (mostly DSL ones) , some of which are patched, some of which are out of support and should be binned.