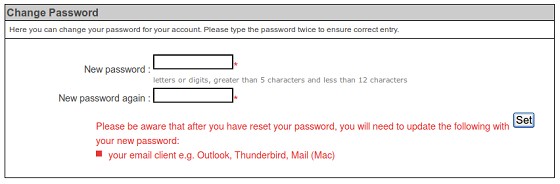
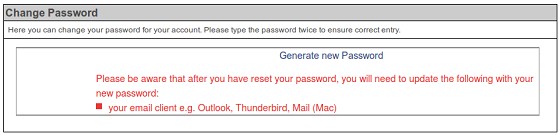
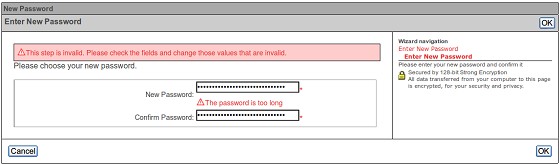
Furthermore, the changes made to Orcon's change password policy don't go far enough. Customers are still limited to less than 12 characters, and passwords cannot contain punctuation or high ANSI characters.
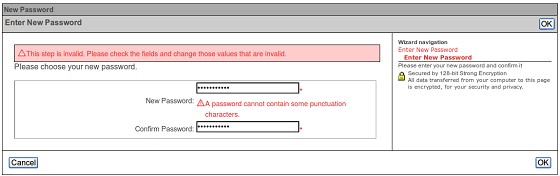
These limited password policies go against Orcon's own recommendations! Their support page recommends that passwords should be at least 8 characters long (no maximum!) and contain a mix of uppercase letters such as A, B, C, lowercase letters such as a, b,c, numerals such as 1, 2, 3, special characters such as $, ?, &, alt characters such as µ, £, Æ.

Why the double standard? Is it possible that Orcon is storing customers' passwords on their side in plaintext? That might explain why they limit the length of our passwords. Hashing a password should reduce and standardise their size on Orcon's end. Come on Orcon, please don't limit the length and complexity of our passwords. According to the Password Strength Calculator, a password limited to less than 12 characters and containing only letters and numbers would provide only 56.9 bits of entropy, which a standard PC could crack within 7 hours!