|
|
|
1101:
I occasionally get IRD emails. I think they may be legit , but id never open them or click on their links .
Emails from IR do not contain links. They say something like "You have [something to attend to/review]. Log into myIR to [see what it is]".
Sometimes I just sit and think. Other times I just sit.
I have saved a couple of these emails and I can confirm that the ones that I have definitely have no personal information in them. All the emails I've seen have been caught by spam filters, and have obvious signs of being scams, e.g. poor spelling and grammar, inconsistent formatting, no personal information, incorrect from addresses, links going to unknown websites, etc.
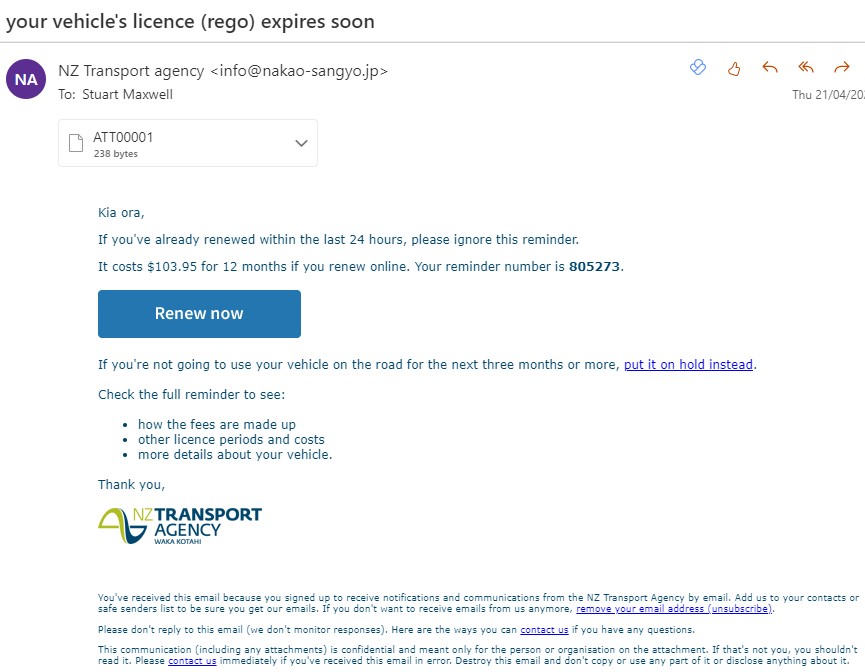
Here's one example - sent from a Japan email domain, and the links take you to Russian domains. Poor grammar and spelling in the subject line, but the content looks fairly good.
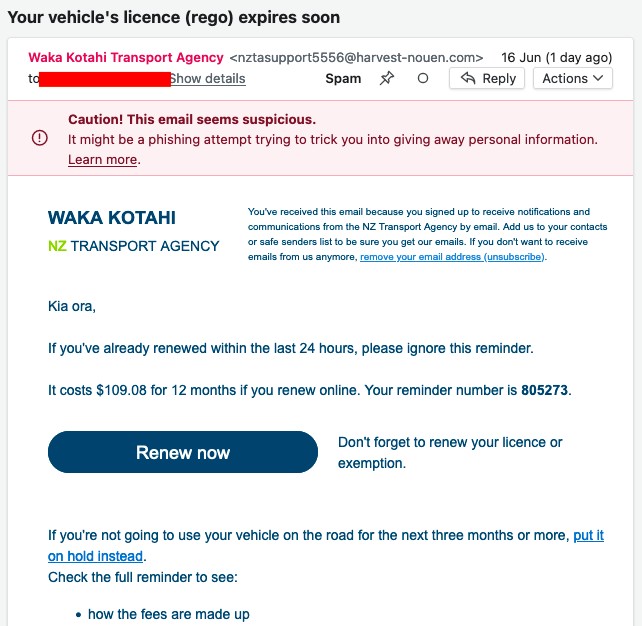
And another one. This one has low-effort content but is using "@nzta.co.nz" domain which may confuse some people.

BlakJak:
I'd expect any actual suggestion that private information has been compromised, to be taken up directly with the agency concerned
We did and were ignored.
Mike
MikeAqua:
BlakJak:
I'd expect any actual suggestion that private information has been compromised, to be taken up directly with the agency concerned
We did and were ignored.
An ongoing question in this thread is whether anyone has had a scam email from Waka Kotahi that contains personal information in it that would imply a system has been compromised. Just coinciding with your car rego expiry date is not an indication of compromise.
Yeap if the above examples where the emails you've been getting then there is zero proof of a PII breach.
MikeAqua:
BlakJak:
I'd expect any actual suggestion that private information has been compromised, to be taken up directly with the agency concerned
We did and were ignored.
Well i'd be interested in details of that.
However if you simply didn't get a personal response to your report, that's not the same as being ignored... i'd suggest they get a lot of reports.
And so far we're talking about bad guys who have a database of email addresses, but that doesn't indicate the compromise of any private information from within NZTA or any other agency.
And for context: I work for another government agency in a cybersecurity capacity and have direct relationships with many of my counterparts - including Waka Kotahi. I can't speak for them but I can connect directly with them and i'm familiar with the standard practices common with most agencies.
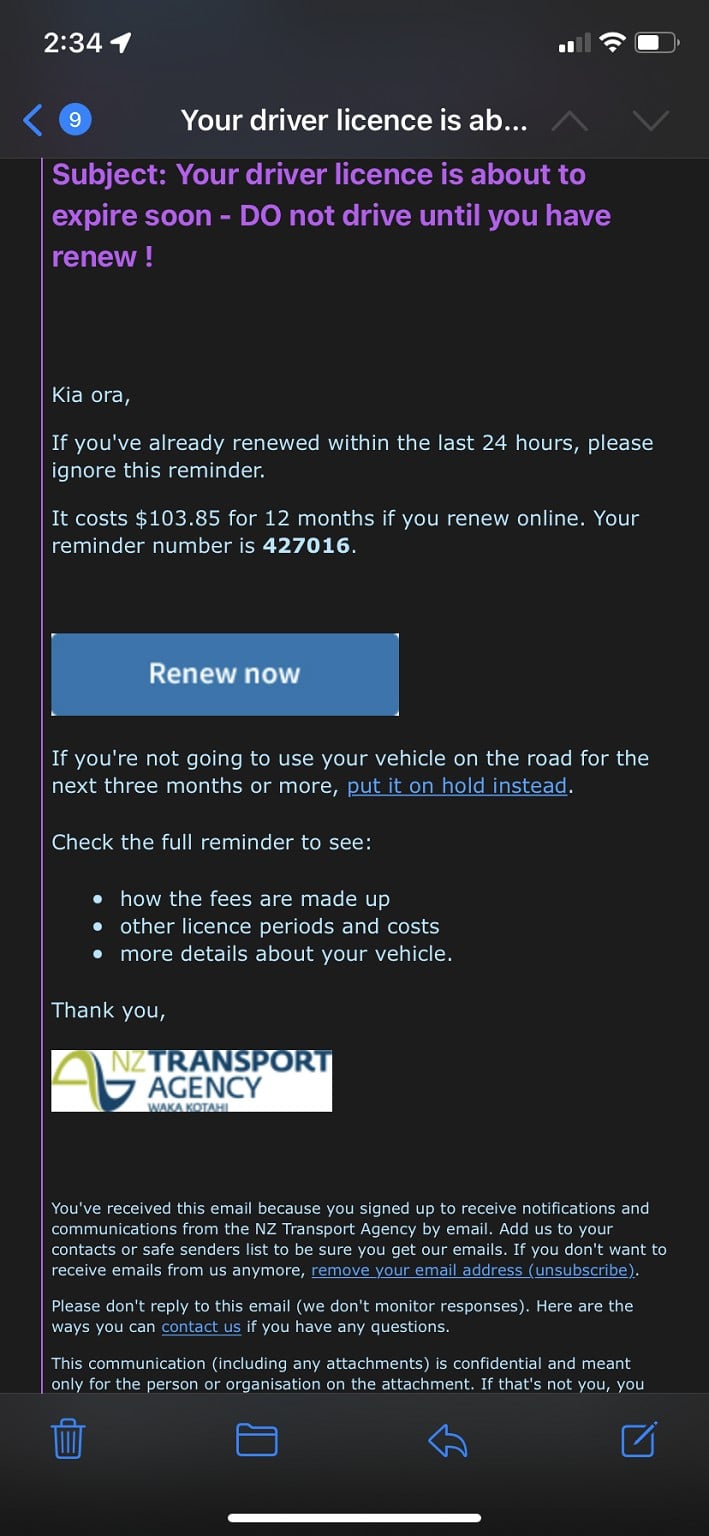
These emails have been around for some time now. In a thread somewhere on here I know I was almost fooled by a very professional email and fake NZTA web site way back in Feb 2020. It was extremely well done with a web site crafted to look like the Waka Kotahi one and no typos or grammatical errors. At the time, the only thing that tipped me off was being asked for my driver's licence number.
I've got a couple of recent ones a few weeks ago, but they look amateur in comparison and have automatically gone to my SPAM folder.
amanzi:
An ongoing question in this thread is whether anyone has had a scam email from Waka Kotahi that contains personal information in it that would imply a system has been compromised. Just coinciding with your car rego expiry date is not an indication of compromise.
Both had the correct rego numbers. Would that indicate compromise? Maybe not as I just checked and >2,000 individuals or organisations have access to the motor vehicle register.
We emailed NZTA, and also called them. The response was a standard comms script that said they hadn't had any security breach and it was just part of general scam.
I actually thought of posting the emails here at the time, but decided I was probably incorrect in my suspicions.
Mike
Pishing email below. Note Fastmail correctly flags this email as a pishing email.
An actual NZTA email here for comparison:
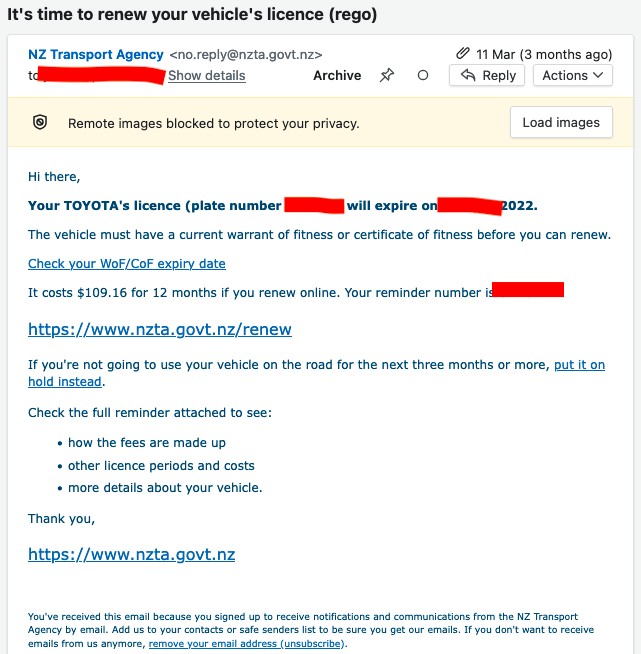
Seems to be some effort to copy e.g. the font colour and some of the text. But lot of giveaways in the pishing email and email providers with good spam filtering system should pick up on some major red flags.
amanzi:
Here's one example - sent from a Japan email domain, and the links take you to Russian domains. Poor grammar and spelling in the subject line, but the content looks fairly good.
yes i recall now, this was the example of mine
So the *only* thing going for it, is it says 'expires soon' and people have associated it to being a leak?
No Registration. No personal details other than making use of an email harvest (or in case of corp domains repeat mass attempts)
The only thing I see, is 'soon' - to some who pay on 3-6 monthly cycle (or 12) -especially if they made use and got into a similar rotation during the hold as part of covid lockdown. Could be within the next 4 months. The next person might think soon is only a month. The next, 6.
Not a lot to go on there.
|
|
|
