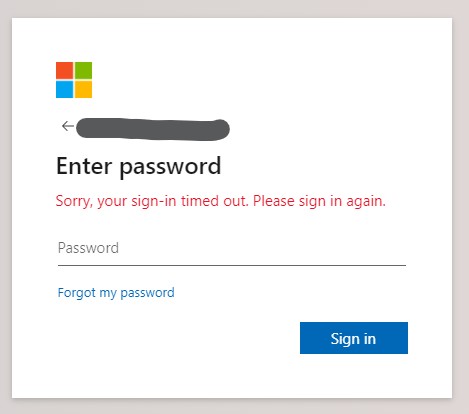
I received my monthly invoice from Voyager today (this was a legitimate email) and then a few hours later I received another invoice from Voyager which looked like a genuine email with my correct name, but an incorrect account number and the monthly fee was too high. The invoice attachment with the email was an HTML file, so I downloaded it, opened in VS Code, and found a bunch of encoded HTML inside a JavaScript script tag. After decoding the HTML, I could clearly see the scam contents which appeared to present an Office 365 logon screen but POSTs the credentials to a PHP script hosted on a Digital Ocean IP address. The logon screen looks and feels like a genuine Office 365 logon prompt, pasted below for your reference.
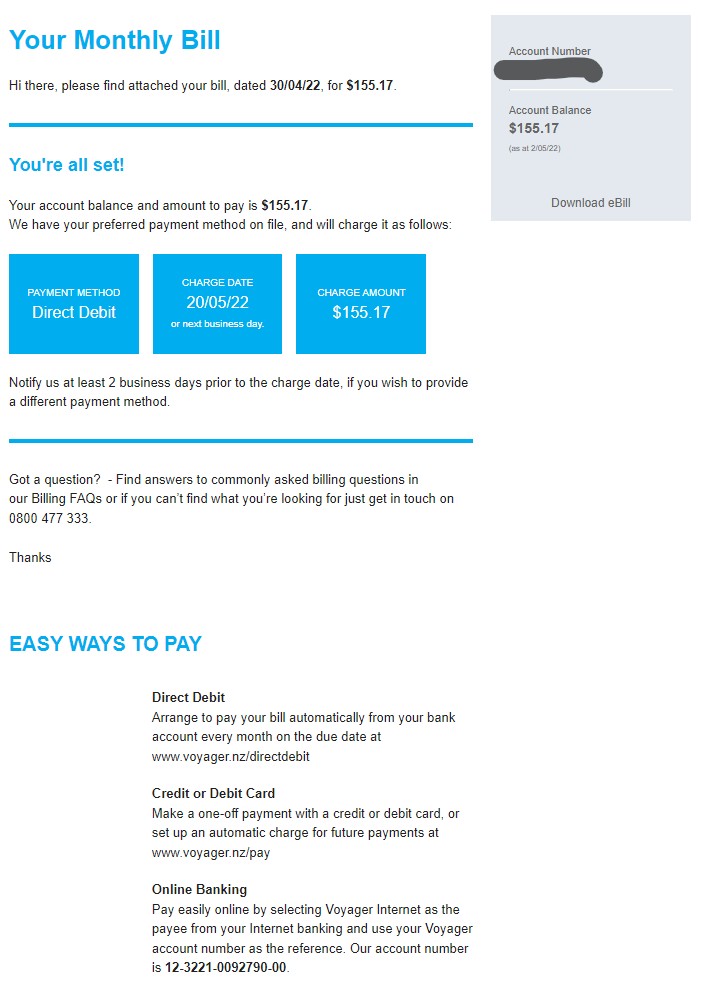
Thought I'd report it here in case other Voyager customers see this and get tricked into trying to open the attachment. Here's a copy of the scam email, I've blanked out the account number because I assume it's a real account number that belongs to another customer. If you're a Voyager customer, you'll recognise this email instantly - looks pretty legit. This is one of the most convincing email scams I've received, and it wasn't picked up by any of the M365 email protections. In fact, on further digging I can see that the SPF checks in the email headers all passed because the email was sent by another M365 customer, whose email must have been hacked.
The logon screen that's presented - this appears after the animation you see when opening Outlook.