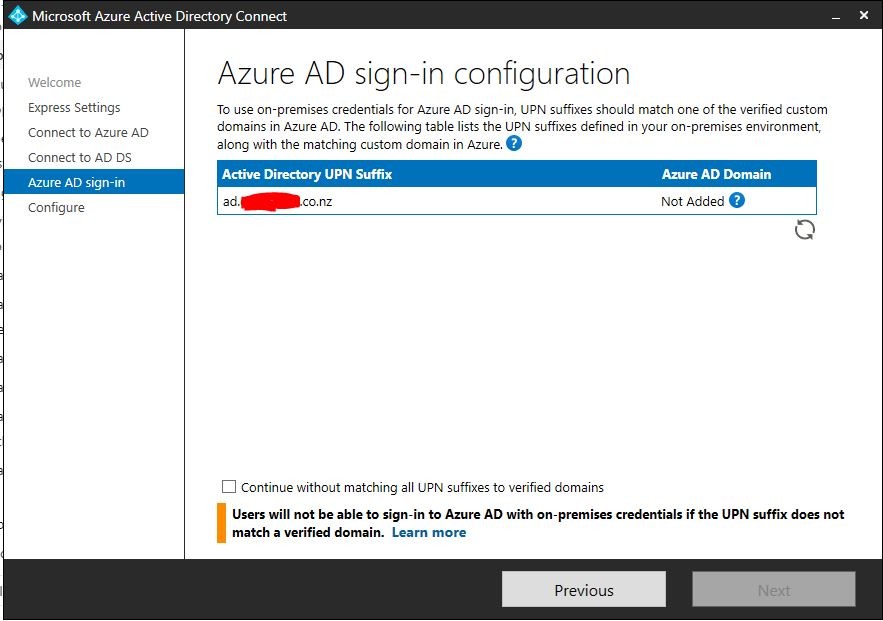
Moving from a fully on premises system to 365 with Hybrid Azure AD. Am doing this as an entirely new internal domain. Haven't used Azure AD Connect before and am hitting a roadblock.
- External domain: domainname.co.nz
- Internal domain: ad.domainname.co.nz
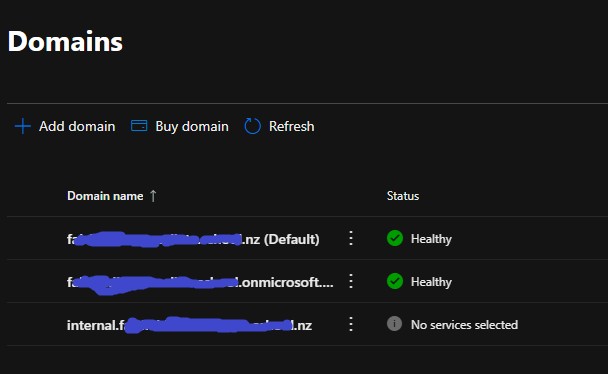
- Have registered domainname.co.nz in 365
- Haven't changed the MX records for the domain as I'm not ready to cut the mail flow over yet.
- Azure AD admin center lists domainname.co.nz as the primary domain.
When I attempt to run the Azure AD Connect on a member server I get the below error. Is this because I created the internal domain as a subdomain, or is it because 365 isn't showing the domain as "healthy" (since I haven't updated the MX records)?
Thanks